Arch Linux on MacBook Pro Retina 2014 with DM-Crypt, LVM and suspend to disk
Warning: This guide is not going to be updated anymore.
[Version française] (/2015/01/arch-linux-sur-macbook-pro-retina-2014-avec-dm-crypt-lvm-et-hibernation) 
Updates
- 2015-12-08 - gummiboot has been integrated to systemd
- 2015-11-06 - section about fan control
- 2015-03-21 - note about Yosemite 10.10.2 update and the gpe66 issue
- 2015-02-27 - workaround for the stuck cursor once back from suspend/hibernate
- 2015-02-07 - fix wrong gummiboot first install command, note about powerdown.git and fstrim
- 2015-01-23 - linux-3.18/broadcom-wl kernel panic fix, cursor stuck when back from hibernation, poweroff after hibernation, systemd/Uswsusp integration
- 2015-01-20 - adding a note about allow-discards root mount option, to forward TRIM commands
- 2015-01-19 - adding a note about the embedded recovery system (from Reddit)
- 2015-01-18 - adding linux-3.18 issue, webcam section, thunderbolt hotplug note (thanks for your comments!)
- 2015-01-17 - typo fixes (thanks to the feedback from the Hacker News thread)
What’s the purpose of this blog post?
This blog post is a kind of checklist, since it was a really time-consuming task to browse many websites to have a big picture and the all the technical details.
I hope this will be useful to someone else.
English is not my native language, corrections and fixes will be greatly appreciated.
Note: This blog post is going to be updated. Only the base install section is finished yet.
I’m going to describe steps needed to have the following system:
- Dual-boot with Arch Linux / Mac OS X
- Boot manager UEFI systemd-boot (formerly Gummiboot) simple, can handle several kernels easily
- Full disk encryption (Mac OS X and Arch Linux)
- LVM support
- Suspend to disk using a swapfile
- Settings for a great battery life (~09h30)
I keep the Mac OS X partition, to be able to update the firmware later.
Warning: don’t blindly copy/paste the commands, especially the ones related to devices /dev/sd *, which are specific to your setup, like the locale and the keyboard mapping. You may lose data.
The MacBook
After wandering for weeks to find a suitable replacement to my old Thinkpad T43, I’ve noticed that MacBook prices were not as crazy as they were before, given the parts and the assembling quality, so I bought one on the Apple refurb for 1279€
I’ve made the decision to buy as much RAM as possible, because it’s soldered and non-upgradeable, and a smaller SSD to stay at a reasonable price.
Hopefully in a few months compatible SSD for this MacBook Pro model will be released, and it’s not going to take a long time to do the upgrade MacBook Pro 13" Retina Display Mid 2014 SSD Replacement
Specifications:
- MacBook Pro Retina 13" mid-2014 (model MacBookPro11,1)
- Intel Core I7 3Ghz
- 16 GB Ram
- 128 GB SSD
- Intel Iris GPU, 1536 MB vram
- 13,3" Retina display 2560x1600
- FaceTime HD webcam 720p
lspci output:
00:00.0 Host bridge: Intel Corporation Haswell-ULT DRAM Controller (rev 09)
00:02.0 VGA compatible controller: Intel Corporation Device 0a2e (rev 09)
00:03.0 Audio device: Intel Corporation Haswell-ULT HD Audio Controller (rev 09)
00:14.0 USB controller: Intel Corporation 8 Series USB xHCI HC (rev 04)
00:16.0 Communication controller: Intel Corporation 8 Series HECI #0 (rev 04)
00:1b.0 Audio device: Intel Corporation 8 Series HD Audio Controller (rev 04)
00:1c.0 PCI bridge: Intel Corporation 8 Series PCI Express Root Port 1 (rev e4)
00:1c.1 PCI bridge: Intel Corporation 8 Series PCI Express Root Port 2 (rev e4)
00:1c.2 PCI bridge: Intel Corporation 8 Series PCI Express Root Port 3 (rev e4)
00:1c.4 PCI bridge: Intel Corporation 8 Series PCI Express Root Port 5 (rev e4)
00:1c.5 PCI bridge: Intel Corporation 8 Series PCI Express Root Port 6 (rev e4)
00:1f.0 ISA bridge: Intel Corporation 8 Series LPC Controller (rev 04)
00:1f.3 SMBus: Intel Corporation 8 Series SMBus Controller (rev 04)
02:00.0 Multimedia controller: Broadcom Corporation Device 1570
03:00.0 Network controller: Broadcom Corporation BCM4360 802.11ac Wireless Network Adapter (rev 03)
04:00.0 SATA controller: Marvell Technology Group Ltd. 88SS9183 PCIe SSD Controller (rev 14)
Base install
Backup
Note: It’s still possible to restore Mac OS X even if the hard drive is completely wiped with the embedded recovery system (Reddit thread)
Since I’m a newcomer to the Mac world, I prefer being safe and take a full backup before playing with encryption or the partitions table (no recovery DVD?)
The backup will be stored on an external USB hard drive, with the MacBook started on an Arch Linux bootable USB key. The whole SSD is copied using the dd command.
- Prepare an USB Arch Linux bootable key
- Boot on the UEFI boot manager (hold the right Alt key)
- Plug the external USB hard drive, dump the whole /dev/sda disk with the dd command
- Reboot to Mac OS X to apply updates
Mac OS X: disk partitioning and encryption
Start the diskutil tool to shrink the only existing partition. I’ve reduced it to 40GB, which leaves 10GB free for Mac OS X, and 81GB for Arch Linux.
Then enable FileVault disk encryption: System preferences -> Security
The Mac OS X partition is now encrypted, and some disk space has been freed for Arch Linux.
A useful link if you can’t resize the partition anymore because of Core Storage vs HFS+ partition type.
Official FileVault Documentation
Arch Linux bootable USB key
Preparing the bootable USB key is straighforward:
wget http://archlinux.mirrors.ovh.net/archlinux/iso/2015.01.01/archlinux-2015.01.01-dual.iso
dd if=archlinux-2015.01.01-dual.iso of=/dev/xx bs=4M
Boot on the USB key (hold the right Alt key), then choose the EFI boot entry:
To get a bigger font, and eventually change the keyboard layout:
setfont sun12x22
loadkeys fr
Network
Internet access is mandatory during the setup to fetch the packages, you have the following choices:
- Connection sharing through USB tethering
- Wireless
- Thunderbolt ethernet adapter
Since I don’t have the Thunderbolt adapter, I will only explain the two other methods. You have to setup the network before further install steps (pacstrap, …)
USB tethering
The easiest way, everything is explained in the Arch Linux wiki. Successfully tested with a Samsung Ace2.
Wireless
The wireless card (pci 14e4:43a0 rev 03) needs a proprietary Broadcom driver, provided by the broadcom-wl package.
The easiest way to build this package is to have around another Arch Linux installation with the same kernel version the setup iso has (3.17.6-1-ARCH):
Steps to build the package:
$ wget https://aur.archlinux.org/packages/br/broadcom-wl/broadcom-wl.tar.gz
$ tar xf broadcom-wl.tar.gz
$ cd broadcom-wl/
$ makepkg -s
Then you have to copy the broadcom-wl-6.30.223.248-4-x86_64.pkg.tar.xz to a second USB key. Once the live Arch Linux USB system has started, mount this key and install the package:
mkdir /tmp/usb
mount /dev/sdd1 /tmp/usb
pacman -U /tmp/usb/broadcom-wl-6.30.223.248-4-x86_64.pkg.tar.xz
In case you only have once USB key, with some efforts you can build our own version with the package integrated.
After the package installation, load the kernel modules needed to connect to a WPA2 wireless network (a wlp3s0 network interface will be appear):
modprobe wl lib80211_crypt_tkip
Then connect to the wireless network with the wifi-menu command.
Arch Linux disk partitioning
Only one partition will be created, which will be encrypted and used as a physical volume by LVM, the latter can hold as many logical volumes as needed.
No partition dedicated to /boot is mandatory, because the boot manager systemd-boot can read and use kernels images and initramfs files stored on the existing ESP partition (usually /dev/sda1)
The SSD uses the GPT format, so we have to use cgdisk instead of fdisk/cfdisk.
cgdisk /dev/sda
The current partition table:
Part. # Size Partition Type Partition Name
-------------------------------------------------------
3.0 KiB free space
1 200.0 MiB EFI System EFI System Partition
2 37.3 GiB Apple Core Storage Macintosh HD
3 619.9 MiB Apple Boot Recovery HD
74.9 GiB free space
There is a debate about the 128MiB gap between partitions: is it mandatory or not? After some research, I’ve found an official explanation:
Note: We leave free space after each partition to make it easier for future system software to manipulate the partition map in ways that we can’t anticipate currently.
If you want to follow the advice, just type +128M when you create a new partition in cgdisk, and are asked for the first sector of the partition.
It’s up to you to leave this gap or not, I’ve decided not to waste my free disk space, and I have not encountered any issue so far, neither with Mac OS X nor Arch Linux.
The final partition table:
Part. # Size Partition Type Partition Name
-------------------------------------------------------
3.0 KiB free space
1 200.0 MiB EFI System EFI System Partition
2 37.3 GiB Apple Core Storage Macintosh HD
3 619.9 MiB Apple Boot Recovery HD
4 74.9 GiB Linux filesystem archlinux
DM-Crypt and LVM
/dev/sda4 partition is going to be encrypted with DM-Crypt, and LVM used over the encryption. It’s called LVM on LUKS, see the wiki page for pros and cons.
Some links to get guidance on the various available algorithms.
I chose the fastest ones given by the cryptsetup benchmark command. If my MacBook gets lost, my goal is not to be worried about my passwords/personal data being in the wild in cleartext,
I don’t care about supercomputers brute force analysis.
If you feel concerned about the full disk encryption overhead (like I was), here is a detailled benchmark.
As far as I’m concerned, with DM-Crypt and ext4 the overhead is insignificant.
# Tests are approximate using memory only (no storage IO).
PBKDF2-sha1 1233618 iterations per second
PBKDF2-sha256 824352 iterations per second
PBKDF2-sha512 627138 iterations per second
PBKDF2-ripemd160 734296 iterations per second
PBKDF2-whirlpool 270251 iterations per second
# Algorithm | Key | Encryption | Decryption
aes-cbc 128b 679,8 MiB/s 2933,1 MiB/s
serpent-cbc 128b 89,1 MiB/s 582,5 MiB/s
twofish-cbc 128b 190,5 MiB/s 370,5 MiB/s
aes-cbc 256b 501,4 MiB/s 2244,5 MiB/s
serpent-cbc 256b 89,9 MiB/s 582,2 MiB/s
twofish-cbc 256b 192,0 MiB/s 370,3 MiB/s
aes-xts 256b 2548,1 MiB/s 2539,2 MiB/s
serpent-xts 256b 582,2 MiB/s 564,1 MiB/s
twofish-xts 256b 359,5 MiB/s 365,8 MiB/s
aes-xts 512b 1956,8 MiB/s 1951,9 MiB/s
serpent-xts 512b 582,7 MiB/s 563,9 MiB/s
twofish-xts 512b 359,7 MiB/s 365,2 MiB/s
Encryption of the partition dedicated to Arch Linux:
$ cryptsetup -v --cipher aes-xts-plain64 --key-size 256 -y luksFormat /dev/sda4
Note: It was needeed to start partprobe for the partition /dev/sda4 to be visible.
Here we open the DM-Crypt device, create LVM physical and logical volumes, and format the partition with ext4 filesystem (which will be used as the root mount point)
$ cryptsetup luksOpen /dev/sda4 lvm
$ pvcreate /dev/mapper/lvm
$ vgcreate vgcrypt /dev/mapper/lvm
$ lvcreate --extents +100%FREE -n root vgcrypt
$ mkfs.ext4 /dev/mapper/vgcrypt-root
Mount the partitions before starting Arch Linux installation:
$ mount /dev/mapper/vgcrypt-root /mnt
$ mkdir /mnt/boot
$ mount /dev/sda1 /mnt/boot
Setup the base Arch Linux system, create /etc/fstab, and add discard option because it’s a SSD:
$ pacstrap /mnt base base-devel
$ genfstab -L -p /mnt >> /mnt/etc/fstab
# /etc/fstab
/dev/mapper/vgcrypt-root / ext4 discard,rw,relatime,data=ordered 0 1
It’s wise to install the wireless adapter driver in our future Arch Linux system, so we will have Internet access on our new system (copied like before from the second USB key):
$ cp /tmp/usb/broadcom-wl-6.30.223.248-4-x86_64.pkg.tar.xz /mnt/root/
$ arch-chroot /mnt
$ pacman -U /root/broadcom-wl-6.30.223.248-4-x86_64.pkg.tar.xz
$ pacman -Sy wpa_supplicant dialog
The next steps are the usual ones from the installation guide, just bear in mind to stop before the bootloader installation:
echo myhostname > /etc/hostname
ln -sf /usr/share/zoneinfo/Europe/Paris /etc/localtime
vi /etc/locale.gen
locale-gen
echo LANG=fr_FR.UTF-8 > /etc/locale.conf
# /etc/vconsole.conf
KEYMAP=fr-latin1
FONT=sun12x22
Update /etc/mkinitcpio.conf to take into account disk encryption and LVM:
HOOKS="base udev autodetect modconf block consolefont keymap keyboard encrypt lvm2 filesystems fsck"
The purpose of each hook is described here
Update the initramfs image:
$ mkinitcpio -p linux
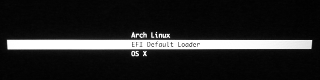
Boot manager systemd-boot
The boot menu is simple and bloat free:
Install, creation of the default options file:
$ mkdir -p /boot/loader/entries
# /boot/loader/loader.conf
default arch
timeout 4
Ensure the ESP partition /dev/sda1 is mounted on the /boot of the chroot, which is from the live system point-of-view /mnt/boot
$ findmnt /boot/
TARGET SOURCE FSTYPE OPTIONS
/boot systemd-1 autofs rw,relatime,fd=24,pgrp=1,timeout=300,minproto=5,maxproto=5,direct
/boot /dev/sda1 vfat rw,relatime,fmask=0022,dmask=0022,codepage=437,iocharset=iso8859-1,shortname=mixed,errors=remount-ro
# Final tree
$ tree /boot/
/boot/
├── EFI
│ ├── APPLE
│ │ ├── EXTENSIONS
│ │ │ └── Firmware.scap
│ │ └── FIRMWARE
│ │ └── MBP111_0138_B15_LOCKED.scap
│ ├── Boot
│ │ └── BOOTX64.EFI
│ └── systemd
│ └── systemd-bootx64.efi
├── initramfs
├── initramfs-linux-fallback.img
├── initramfs-linux.img
├── loader
│ ├── entries
│ │ ├── arch.conf
│ │ └── devel.conf
│ └── loader.conf
├── System.map
└── vmlinuz-linux
Add a new entry for our Arch Linux install:
# /boot/loader/entries/arch.conf
title Arch Linux
linux /vmlinuz-linux
initrd /initramfs-linux.img
options cryptdevice=/dev/sda4:vgcrypt:allow-discards root=/dev/mapper/vgcrypt-root rw
Details:
- Paths are relative to /boot/
- options cryptdevice=/dev/sda4:vgcrypt:allow-discards root=/dev/mapper/vgcrypt-root rw
- /dev/sda4 is the encrypted partition containing the LVM physical volume
- vgcrypt is the LVM volume group
- allow-discards forward TRIM commands from encryption layer to device (security implication)
- root=/dev/mapper/vgcrypt-root is the LVM logical volume where / is mounted
- rw
Mount root device read-write on boot
More information about the options line here
Systemd-boot initial setup:
$ bootctl install
Copied "/usr/lib/systemd/boot/efi/systemd-bootx64.efi" to "/boot/EFI/systemd/systemd-bootx64.efi".
Copied "/usr/lib/systemd/boot/efi/systemd-bootx64.efi" to "/boot/EFI/Boot/BOOTX64.EFI".
Created EFI boot entry "Linux Boot Manager".
The base system install is finished!
After a reboot, the systemd-boot menu will appear, and you have to enter the password for DM-Crypt.
Wireless networking is working with the wifi-menu command. It is wise to use the package broadcom-wl-dkms instead of broadcom-wl if you use a custom kernel.
Suspend to disk (Uswsusp)
Here is a comparison of the different suspend to disk solutions. I’m going to use Uswsusp because of its support for swapfiles (in addition to swap partitions)
Installation of the uswsusp-git package:
aurget -S swsusp-git
Create a 8 GiB swapfile (I rely on uswusp compression)
$ fallocate -l 8G /swapfile
$ chmod 600 /swapfile
$ mkswap /swapfile
Add the swapfile to /etc/fstab, tune the VM system to use it as little as possible (I have 16 GiB of ram), and swapfile activation:
# /etc/fstab
/swapfile swap swap defaults 0 0
# /etc/sysctl.d/99-disable-swapfile.conf
vm.swappiness=1
$ swapon -a
The uswusp-git package post-install note gives some interesting information, which we are going to follow:
==> The new Software Suspend does not use kernel parameters
==> to determine the suspend partition, instead it consults
==> /etc/suspend.conf when booting.
==> You MUST edit this file before you update your initrd.
==> Point the "resume device" variable to your swap partition.
==> You will need to update your mkinitcpio.conf file to
==> include the hook uresume. Replace your 'resume' hook
==> with 'uresume'. If you do not have a resume hook the
==> uresume hook must go before filesystems but after block.
==> Do not get this wrong. Then rebuild the ramdisk with
==> '# mkinitcpio -p linux' (or what else needed for the
==> kernel you use)
Grab the offset of the swapfile:
$ swap-offset /swapfile
resume offset = 149504
Edit the configuration file of suspend to disk:
# /etc/suspend.conf
snapshot device = /dev/snapshot
resume device = /dev/mapper/vgcrypt-root
resume offset = 149504 # offset of /swapfile
image size = 8589934592 # size of /swapfile
compress = y
splash = n
resume pause = 5 # 5s to read ram dump/restore stats
threads = y
shutdown method = shutdown # power off instead of rebooting after entering into hibernation
Add the uresume hook after encrypt, lvm2 and before filesystems (the order really matters)
# /etc/mkinitcpio.conf
HOOKS="base udev autodetect modconf block consolefont keymap encrypt lvm2 uresume filesystems keyboard fsck"
Update the initramfs image:
$ mkinitcpio -p linux
Tell systemd to use s2disk through systemd-hibernate (wiki entry)
# cp /usr/lib/systemd/system/systemd-hibernate.service /etc/systemd/system/
# cd /etc/systemd/system/
# edit systemd-hibernate.service and replace the ExecStart line with
ExecStart=/bin/sh -c 's2disk'
Now the MacBook can be suspended to disk with the systemctl hibernate command. For suspend to ram, just close the lid, or use the systemctl suspend command.
Post-installation
Just a few notes, because many things are already documented in the dedicated 11,1 MacBook model wiki page.
Power saving
With these settings, I reach almost 09h30 of battery life, not that bad compared to Mac OS X.
Note: some people have suggested through the comments powerdown.git as a good way to improve battery life (not tested yet)
Powertop
To apply automatically optimal settings at boot (GOOD in the tunables tab)
Create a new Systemd unit:
# /etc/systemd/system/powertop.service
[Unit]
Description=Powertop tunings
[Service]
Type=oneshot
ExecStart=/usr/bin/powertop --auto-tune
[Install]
WantedBy=multi-user.target
Enable at each boot:
$ systemctl enable powertop.service
GPU
File /etc/modprobe.d/i915.conf
options i915 enable_rc6=1 enable_fbc=1 lvds_downclock=1
More information about the GPU power states you can see in Powertop here
Warning: you may experience some issues (lockup, no backlight, …) with these options after coming back from suspend to disk.
Intel audio chipset
/etc/modprobe.d/snd_hda_intel.conf
options snd_hda_intel power_save=1
USB
/etc/modprobe.d/usbcore.conf
options usbcore autosuspend=1
Keyboard: special keys
- Screen brightness
- Keyboard brightness
- Sound level
With xbindkeys and ~/.xbindkeysrc file:
# xbacklight and kbdlight (AUR) needed
"amixer set Master playback 5%+"
XF86AudioRaiseVolume
"amixer set Master playback 5%-"
XF86AudioLowerVolume
"amixer set Master toggle"
XF86AudioMute
"xbacklight -dec 10"
XF86MonBrightnessDown
"xbacklight -inc 10"
XF86MonBrightnessUp
"kbdlight up"
XF86KbdBrightnessUp
"kbdlight down"
XF86KbdBrightnessDown
xbindkeys must be started at the beginning of your X session (.xinitrc, …)
Note: It is possible to automatically adjust brightness using the MacBook built-in ambient light sensor, with lighter or lightum
Touchpad
There is more advanced driver for the touchpad than the default synaptics one, xf86-input-mtrack
Installation:
aurget -S xf86-input-mtrack.git
All directives are explained in the project README, below are my settings:
# /etc/X11/xorg.conf.d/60-mtrack.conf
Section "InputClass"
Identifier "touchpad"
Driver "mtrack"
MatchIsTouchpad "on"
MatchDevicePath "/dev/input/event*"
Option "Sensitivity" "0.65"
Option "TapButton1" "0"
Option "TapButton2" "2"
Option "TapButton3" "0"
Option "TapButton4" "0"
Option "ClickFinger1" "1"
Option "ClickFinger2" "0"
Option "ClickFinger3" "0"
Option "ButtonMoveEmulate" "false"
Option "FingerHigh" "10"
Option "FingerLow" "1"
Option "IgnoreThumb" "true"
Option "IgnorePalm" "true"
Option "TapDragEnable" "false"
EndSection
Resolved issues
I’ve faced these issues at the time of my initial Arch Linux installation, with archlinux-2015.01.01-dual.iso media and default kernel 3.17.6-1-ARCH.
You might not encounter them with more recent versions or a slightly different MacBook.
Kernel panic with linux 3.18 (wireless driver)
Note: This has been fixed in the latest version of broadcom-wl package (6.30.223.248-5)
Upgrading to linux 3.18 and using the proprietary broadcom-wl driver leads to a kernel panic for many people. It is better to stick with linux 3.17 for the time being.
Console font is partially applied
Despite a correct font configuration in /etc/vconsole.conf, the console font at the login prompt is barely readable, but was bigger at the earlier DM-Crypt password prompt.
This is because of kernel mode setting, you have to load the i915 kernel module earlier, to avoid the display flip.
Add i915 in the MODULES list of /etc/mkinitcpio.conf:
MODULES="i915"
Then update your initramfs image.
High CPU usage
Note: It appears to be fixed by the Yosemite 10.10.2 update (more details in the comments)
The MacBook gets warm pretty quickly without any apparent reason, and the battery life is very low (~2h30).
A kernel thread kworker uses a lot of CPU:
PID UTIL. PR NI VIRT RES %CPU %MEM TEMPS+ S COM.
39 root 20 0 0,0m 0,0m 70,7 0,0 0:55.59 R kworker/0:2
And many ACPI related interrupts in powertop:
Usage Events/s Category Description
75,6 ms/s 6655,9 Interrupt [9] acpi
86,3 ms/s 4627,4 kWork acpi_os_execute_deferred
Fix: echo "disable" > /sys/firmware/acpi/interrupts/gpe66
Systemd unit to enable the command at system boot:
# /etc/systemd/system/suppress-gpe66.service
[Unit]
Description=Disables GPE 66, an interrupt that is going crazy on Macs
[Service]
ExecStart=/usr/bin/bash -c 'echo "disable" > /sys/firmware/acpi/interrupts/gpe66'
[Install]
WantedBy=multi-user.target
Activation:
systemctl enable suppress-gpe66.service
ata errors
Dreadful messages appearing in dmesg
[ 527.246778] ata1: exception Emask 0x10 SAct 0x0 SErr 0x10000 action 0xe frozen
[ 527.246839] ata1: irq_stat 0x00400000, PHY RDY changed
[ 527.246876] ata1: SError: { PHYRdyChg }
[ 527.246906] ata1: hard resetting link
[ 527.963651] ata1: SATA link up 6.0 Gbps (SStatus 133 SControl 300)
[ 527.964126] ata1.00: unexpected _GTF length (8)
[ 527.964803] ata1.00: unexpected _GTF length (8)
[ 527.964926] ata1.00: configured for UDMA/133
[ 527.965030] ata1: EH complete
However I’ve not found so far any issue…
Default sound output through HDMI
I’m using Alsa, and by default the sound goes through the HDMI output, and not through the Intel chipset (Cirrus Logic CS4208).
To change this behavior, the option index=1,0 has to be passed to the kernel module snd-hda-intel:
# /etc/modprobe.d/snd_hda_intel.conf
options snd-hda-intel index=1,0
Mouse cursor stuck when back from hibernation/suspend
The mouse cursor works fine when returning from suspend, but gets stuck when returning from hibernation.
Using xinput we can see that the touchpad device status becomes floating slave.
$ xinput
⎡ Virtual core pointer id=2 [master pointer (3)]
⎜ ↳ Virtual core XTEST pointer id=4 [slave pointer (2)]
⎣ Virtual core keyboard id=3 [master keyboard (2)]
↳ Virtual core XTEST keyboard id=5 [slave keyboard (3)]
↳ Video Bus id=7 [slave keyboard (3)]
↳ Power Button id=8 [slave keyboard (3)]
↳ Power Button id=6 [slave keyboard (3)]
↳ Sleep Button id=9 [slave keyboard (3)]
↳ Apple Inc. Apple Internal Keyboard / Trackpad id=10 [slave keyboard (3)]
~ bcm5974 id=11 [floating slave]
Reattaching the device with xinput –enable bcm5974 or reloading bcm5974 kernel module does the trick.
Driver bug entry, forum thread
Workaround (thanks to Chase Colman)
Create the following new systemd unit in /etc/systemd/fixtrackpad@.service
[Unit]
Description=Fix trackpad after resume
After=suspend.target
After=hibernate.target
[Service]
User=%I
Type=simple
Environment=DISPLAY=:0
ExecStart=/usr/bin/xinput -enable bcm5974
[Install]
WantedBy=suspend.target
WantedBy=hibernate.target
Enable it for your user (replace loic here)
$ systemctl enable fixtrackpad@loic.service
The cursor is now working when back from hibernation or suspend state.
Current issues
Problems without any known workaround, at least for my MacBook model. Your mileage may vary.
No FaceTime webcam driver
Since the switch from USB to PCIe bus, no driver exist for the built-in FaceTime camera.
Thunderbolt hotplug
It is not clear if Thunderbolt adapters must be connected at boot to work.
There is also maybe issues with suspend, but without any adapters to check by myself, I can’t do anything else than asking for your feedback!
Some pointers:
- Thunderbolt and other Macbook hardware issues with Linux
- Playing with Thunderbolt under Linux on Apple hardware
- Phoronix: Apple Thunderbolt Driver Might Be Added To Linux 3.16 Kernel
- Kernel commit: Thunderbolt hotplug support over cactus Ridge controller
Fan control
Without any tuning (kernel 4.2.5), the cores temperature can rise pretty high, nearly to the critical limit of 100°c. I can hit 96°C while compiling a Linux kernel.
Dmesg extract:
[ 2697.685014] mce: [Hardware Error]: Machine check events logged
[ 3919.798663] CPU2: Core temperature above threshold, cpu clock throttled (total events = 166)
[ 3919.798664] CPU0: Core temperature above threshold, cpu clock throttled (total events = 166)
[ 3919.798666] CPU3: Package temperature above threshold, cpu clock throttled (total events = 380)
[ 3919.798668] CPU1: Package temperature above threshold, cpu clock throttled (total events = 380)
[ 3919.798668] CPU0: Package temperature above threshold, cpu clock throttled (total events = 380)
[ 3919.798675] CPU2: Package temperature above threshold, cpu clock throttled (total events = 380)
To stay around a more acceptable temperature range, I’ve found that [https://github.com/dgraziotin/mbpfan](mbpfan daemon) does a pretty good job. Of course, the fan is running louder at full load.
# Install mbpfan-git from AUR
$ aurget -S mbpfan-git
# Run the test mode to ensure it will work
$ sudo mbpfan -t
Starting the tests..
It is normal for them to take a bit to finish.
min_fan_speed value is not 6200
Tests run: 6
# Activate at system boot
$ sudo systemctl enable mbpfan.service
With the default mbpfan configuration, when fully loaded the cores temperatures stay around 80°C, which is really more acceptable, and 45°C when idle.
Misc
SSD: delaying TRIM operations
Leonardo has raised in the comments an interesting point: delaying trim operations on the SSD can enhance performances. With the discard option in /etc/fstab, every time you delete a file the SSD do its housekeeping operations in real time.
It is possible to delay these SSD operations with the fstrim tool, that you will have to run periodically (and remove discard option from /etc/fstab by the way).
I have not tested yet, but here is some pointers:
i3-wm: lock the screen when returning back from suspend
I use i3lock. Here is a new Systemd Unit that starts i3lock just before going to suspend:
# /etc/systemd/system/i3lock.service
[Unit]
Description=i3lock
Before=suspend.target
[Service]
User=loic
Type=forking
Environment=DISPLAY=:0
ExecStart=/usr/bin/i3lock -c 000000
[Install]
WantedBy=suspend.target
Activation:
systemctl enable i3lock.service
Firefox and Retina display
Just install the AutoDiDPI extension to have fonts automatically scaled to something readable.